Öncelikle şunu belirteyim belki içinizde daha önce bunu yapan vardır. IIS teki siteler başka bi IIS e taşınırken tek tek bu uygulamaları tanımlamak bazen işkenceye dönüşebilir. Hele bide benim gibi bir sunucuda 60 – 70 sitenin her birini altında ...
Archives
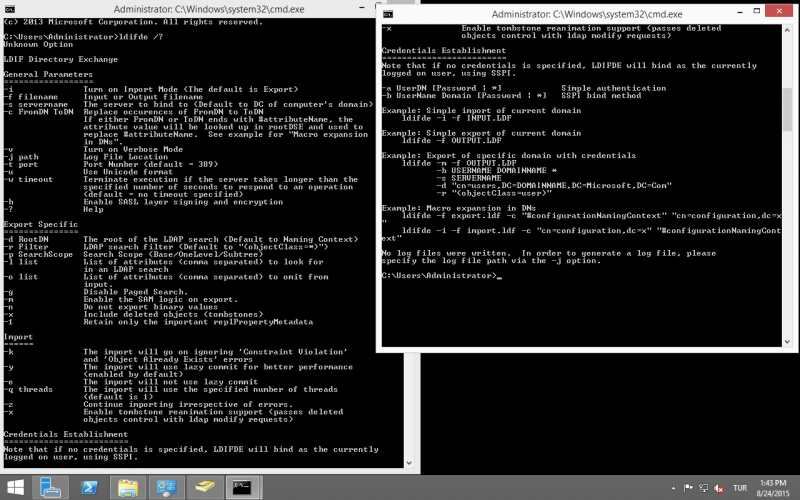
Kısa bir özetle konumuzun tanımını yapmak istiyorum. Günümüz sistemlerinde Active Directory vazgeçilmez bir yer almaktadır. Ve Active Directory de saatlerimizi alabilecek durumlar olabilmektedir. Ve burda bahsetmek istediğim konu LDAP protokolünden CMD aracılığı ile AD deki kullanıcı listesini export yada import ...
Host Dosyasına Kayıt Ekleme
GPO Account Password Ayarlarını Değiştirmek
IIS Server da Process Sayısını Arttırma
Fortigate 5.4.X DNS Sorunu
IIS de Site ve AppPool İmport/Export işlemi
IIS Server da Process Sayısını Arttırma
Fortigate SD WAN Nedir ? Nasıl Kurulur ?
Fortigate Multiple İnterfaces Policies Nedir ?
SQL Server ve Perform Volume Maintenance Task
Fortigate LDAP Authentication
The Hacker News
- Network Threats: A Step-by-Step Attack Demonstrationby [email protected] (The Hacker News) on 25 Nisan 2024 at 11:13
Follow this real-life network attack simulation, covering 6 steps from Initial Access to Data Exfiltration. See how attackers remain undetected with the simplest tools and why you need multiple choke points in your defense strategy. Surprisingly, most network attacks are not exceptionally sophisticated, technologically advanced, or reliant on zero-day tools that exploit
- DOJ Arrests Founders of Crypto Mixer Samourai for $2 Billion in Illegal Transactionsby [email protected] (The Hacker News) on 25 Nisan 2024 at 10:21
The U.S. Department of Justice (DoJ) on Wednesday announced the arrest of two co-founders of a cryptocurrency mixer called Samourai and seized the service for allegedly facilitating over $2 billion in illegal transactions and for laundering more than $100 million in criminal proceeds. To that end, Keonne Rodriguez, 35, and William Lonergan Hill, 65, have been charged
- Google Postpones Third-Party Cookie Deprecation Amid U.K. Regulatory Scrutinyby [email protected] (The Hacker News) on 25 Nisan 2024 at 06:37
Google has once again pushed its plans to deprecate third-party tracking cookies in its Chrome web browser as it works to address outstanding competition concerns from U.K. regulators over its Privacy Sandbox initiative. The tech giant said it's working closely with the U.K. Competition and Markets Authority (CMA) and hopes to achieve an agreement by the end of the year. As part of the
- State-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionageby [email protected] (The Hacker News) on 25 Nisan 2024 at 05:50
A new malware campaign leveraged two zero-day flaws in Cisco networking gear to deliver custom malware and facilitate covert data collection on target environments. Cisco Talos, which dubbed the activity ArcaneDoor, attributing it as the handiwork of a previously undocumented sophisticated state-sponsored actor it tracks under the name UAT4356 (aka Storm-1849 by Microsoft). "
- U.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacksby [email protected] (The Hacker News) on 24 Nisan 2024 at 13:43
The U.S. Treasury Department's Office of Foreign Assets Control (OFAC) on Monday sanctioned two firms and four individuals for their involvement in malicious cyber activities on behalf of the Iranian Islamic Revolutionary Guard Corps Cyber Electronic Command (IRGC-CEC) from at least 2016 to April 2021. This includes the front companies Mehrsam Andisheh Saz Nik (MASN) and Dadeh









Son yorumlar